Meraki in the Enterprise ASTERISK
June 21, 2023 Leave a comment
If two decades in the VAR space teaches you anything, it’s that if you want to challenge yourself, learn to say yes, then qualify the relevance of that “yes” to the proposed question. One of the most heavily asterisk’d responses I’ve had to give in the past is in response to the question, “Is Meraki right for the Enterprise”, and I’m of the opinion that it’s high time we start leaving the asterisk off. Look, I’ve been a proponent of Meraki since prior to the Cisco acquisition, but let’s be honest, I’ve clarified that “asterisk’d Yes” in many ways over the years:
Is Meraki right for the Enterprise? Yes*
Over the years you may recall such greats as:
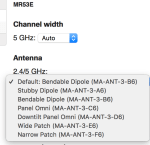
*But they don’t have external antennas, so challenging RF environments are out!
Shortly after acquisition, Meraki did indeed role out External antenna support for their indoor portfolio and it’s been a part of the portfolio since!
*But they don’t have firmware update controls or release notes
Meraki has now one of the best software image management functions available. Or if you’re like most folks, you just want the peace of mind knowing you can refer to it after you’ve set it and forgotten it.
*But they don’t have a way to turn off 2.4GHz radios or have RF profiles so challenging RF environments are still out!
Adoption of RF Profies in the dashboard with no on-premises hardware changes or updates? All delivered seamlessly as part of a dashboard update – and you didn’t have to do anything to get it.
*But they don’t have high gain antennas so challenging RF environments are still still out!
With Smart Antennas, Meraki is able to use the same RP-TNC connectors as other antennas, but this hardware level innovation never got much attention despite the fact that it enabled more complex designs with regulatory compliance assurance.
*But the operating temperature of the AP is on the weak side and I’m concerned that they’ll melt in the rafters long term (or really any other AP centric “quality concern” that could be raised) so challenging RF environments are still still still out!
Meraki adopting the Cisco AP portfolio for a unified approach to the hardware handily assuaged *many* concerns throughout the industry. Meraki APs were fine, but this makes is easy to reconcile for the field. If you can put a Cisco AP in a challenging RF environment, you can put a Meraki AP there now (since they’re the same thing)!.
*But RRM! The Cloud simply can’t do as good of a job at challenging RF environments as my WLCs RRM so challenging RF environments are still still still still out!
At Mobility Field Day, Cisco showed off a unified RRM control plane feature that is a standalone RRM function that either your on premises controllers can use or your Meraki dashboard can use. The goal here is that regardless of the management platform (DNA Center or Meraki dashboard), you should be able to adopt an RRM system that works consistently across both platforms.
*But centralized Data Plane/VLANs/tunneling/<other WLC centric concern here> means I have to abandon the Meraki dashboard, so clearly campus enterprise is out!
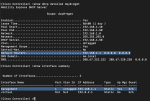
Well, this is one that has been sticking in my craw for years, I’ll admit. It wasn’t until last years Catalyst portfolio transition for the Meraki wireless offering, that I had any hope that we’d see what I call “good” guidance on the topic. This has always left Campus Enterprise customers out in the wind to some degree or another. That was until I saw with my very own eyes Meraki pulling a Catalyst 9800 WLC into the dashboard for monitoring. Now, there’s a lot to unpack here and when I first saw this I had about a billion questions. Like:
1) What do you mean I can have my 9800 controllers in the Meraki cloud?
This one I just had to have clarification on – it finally delivers on a huge part of the Meraki/Catalyst integration and yes, you can simply add your WLCs to the dashboard. You then get AP insights (they look just like a Meraki AP!) and of course all of that delicious client info. In short, add your WLCs to the dashboard and you have instantly massive insight into your clients and infrastructure. All without making any changes on your WLC!
2) I’ve been in the dashboard, and there’s no way I can configure all the same things as I need on my 9800 there. How limited am I going to find myself here?
Well, the good news on that front is that for now, this is monitoring only – you retain all of your 9800 functionality and do all of your configuration still on the 9800 directly – no loss of features since there really isn’t much to do from the dashboard once you’ve added it other than bask in the glory of the insights!
3) Monitor only? What if I want to configure my 9800 from the dashboard and I can’t?
Well yes – that is the current state of the integration – but believe me when I say, the trajectory that Cisco laid out at MFD is clear – Meraki and Catalyst everywhere that DNA Center is “too much”. I think it’s safe to assume that based on the current features available across the EN portfolio (especially on the MS and MR platforms) integrated into the dashboard – that Cisco isn’t done here.
Regardless of where you stand on on your definition of Enterprise requirements (campus or otherwise), it’s clear that if you haven’t been watching the Meraki integrations happening over at Cisco, you really need to spend some time making sure that any of those pesky preconceived blockers you may have in the past aren’t quite so show-stopping now a days…